The Hard Lesson of a Perfectly Segmented Home Network: Why Strict Isolation Isn't Always Practical
Introduction: The Dream of Perfect Segmentation
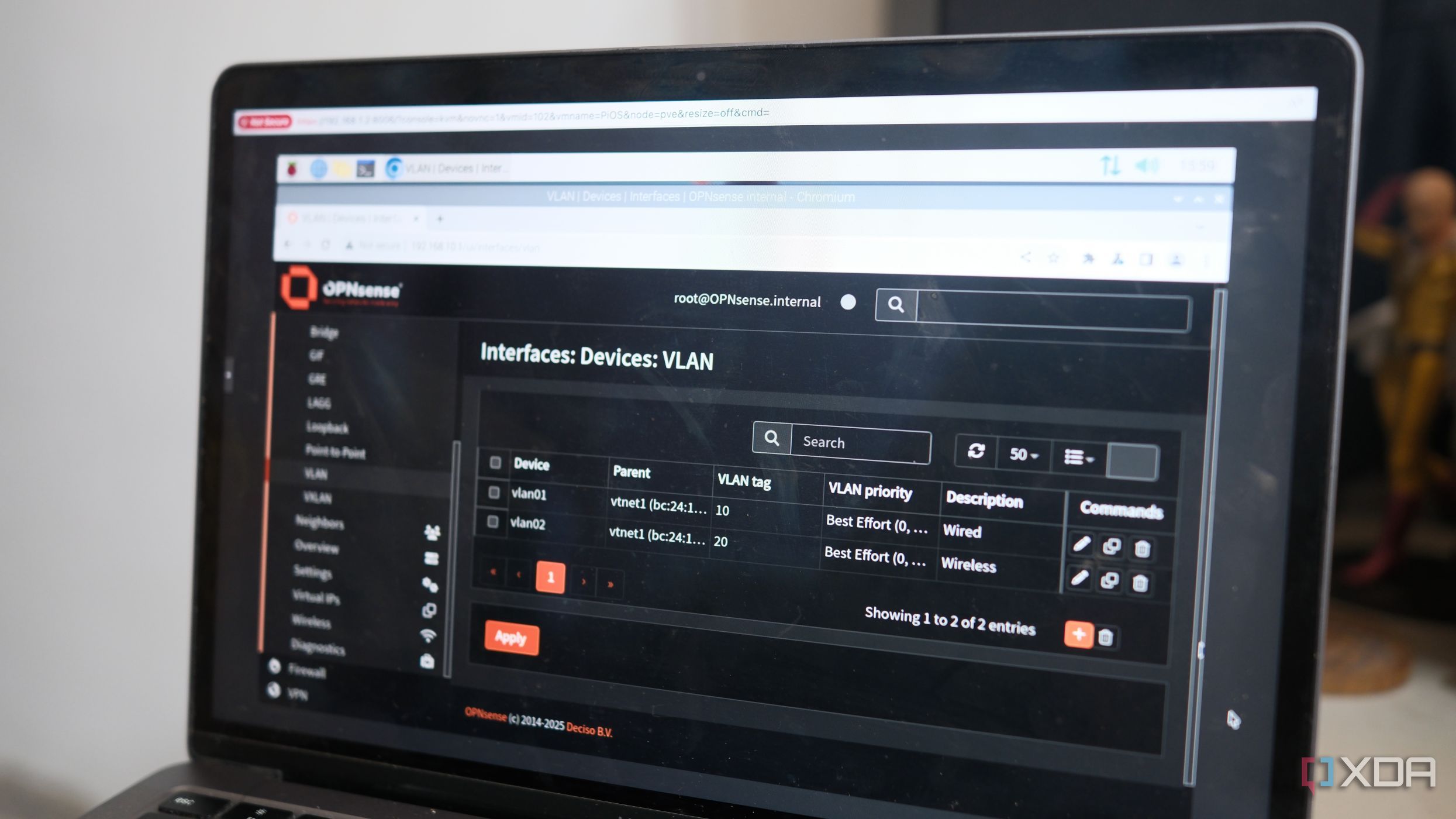
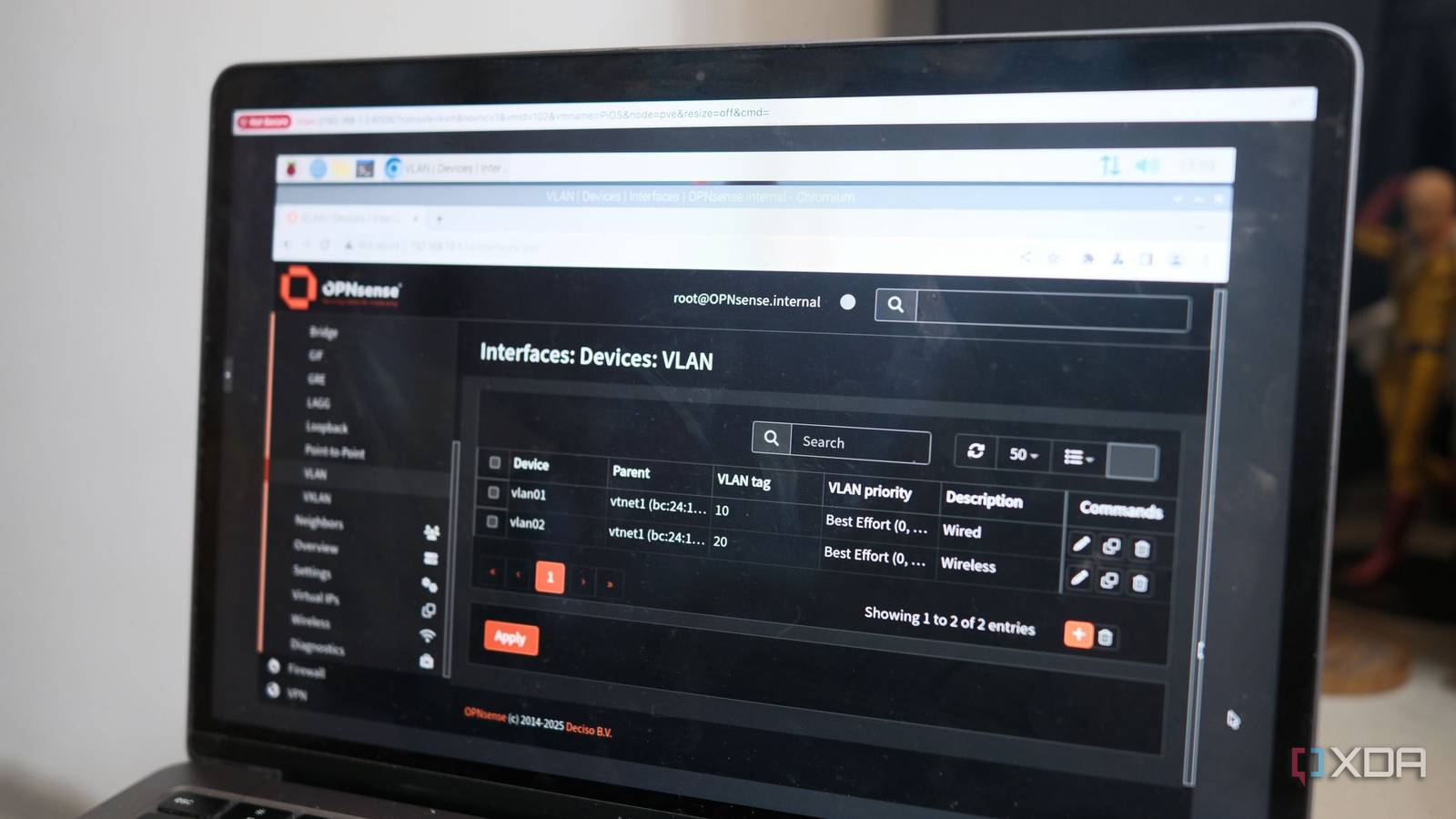
Last year, I embarked on a weekend project that felt like the pinnacle of home network security: I deployed OPNsense on a small form-factor mini PC and carved my home network into airtight VLANs. Internet of Things (IoT) devices were confined to their own subnet, trusted personal machines shared another, and guests were relegated to a third. Each segment was guarded by firewall rules that I crafted with the precision of a network engineer. For a brief moment, I felt invincible.
The Initial Setup: A Fortress of VLANs
Hardware and Software Choices
I chose OPNsense because of its robust firewall capabilities and open-source flexibility. The mini PC, equipped with dual Intel NICs, provided more than enough horsepower for a home network routing several VLANs. I set up three main segments: Trusted (for personal computers and NAS), IoT (for smart bulbs, cameras, and thermostats), and Guest (for visitors with limited internet access).
Firewall Rules and Isolation
Every rule was explicit: IoT devices could only reach their update servers via an allowed port. Trusted devices could initiate connections to the internet, but inbound traffic from IoT was dropped. Guests were confined to HTTP/HTTPS only. I even added an intrusion detection system (IDS) to monitor cross‑VLAN traffic. The network was, by design, a set of silos.
Real‑World Use: When Isolation Becomes a Barrier
Problem #1: The Smart Home Hub
My smart home system – a combination of a Hubitat hub and various Zigbee devices – required periodic access to my media server for event logging and local voice commands. Because the media server lived on the Trusted VLAN and the hub on IoT, the firewall rules I had so carefully crafted blocked that traffic. The result? Automation routines failed, logs went missing, and my wife asked why the lights wouldn't turn off on schedule.
Problem #2: Remote Access to the NAS
I needed to access my NAS (on Trusted) from my laptop (also on Trusted) – that worked fine. But when I wanted to give a family member limited read‑only access to a photo share from their IoT‑connected TV? The firewall stepped in. I had to create a specific rule to allow that one port from IoT to Trusted, but only for the TV’s MAC address.
Problem #3: Guest Access to the Printer
Guest VLAN visitors often wanted to print. My network printer resided on Trusted. After several complaints, I reluctantly added a rule that allowed all guest IPs to reach the printer’s IP on port 9100 (JetDirect). This felt like a crack in the fortress.
The Long Process of “Poking Holes”
Over the next six months, I created dozens of tiny exceptions – what I call “holes” – in my once‑perfect firewall. I started a spreadsheet: allow Harmony Hub to Trusted on port 8080, allow iPhone (Trusted) to IoT camera on port 554 for local streaming, allow Guest to NAS for PDF sharing. Each hole felt like a compromise, yet each was necessary for the network to serve its actual purpose – enabling my family’s daily technology needs.
Lessons Learned: Balancing Security and Usability
Embrace the “Principle of Least Privilege” but With Exceptions
Perfect isolation is a noble goal, but home networks aren’t enterprise data centers. You must allow legitimate cross‑VLAN communication. The key is to document every rule and audit it regularly. I now use aliases and groups in OPNsense to keep the rule set manageable.
Use Application‑Layer Controls
Instead of opening broad ports, I moved to application‑level proxies (e.g., HAProxy for web services) and VPN tunnels for remote access. That way, IoT devices still can’t directly talk to my NAS, but they can reach a proxy that provides limited, authenticated access.
Accept That a Home Network Is a Living System
Segmentation is a process, not a one‑time configuration. When a new smart device arrives, test its needed connectivity and update rules accordingly. I now spend one evening per quarter reviewing and adjusting the firewall.
Conclusion: The Rewards of Pragmatic Segmentation
My network is still segmented – IoT devices cannot initiate connections to Trusted, and guests are sandboxed. But I’ve accepted that perfect segmentation is impossible in a home environment where convenience and compatibility matter. By carefully poking holes where needed, I’ve achieved a balance that protects my privacy without frustrating my family. The weekend project that made me proud taught me that true network security is as much about flexibility as it is about walls.
If you’re building a segmented network, start with strict isolation, but be ready to adjust. Your life – and your spouse – will thank you.
Related Articles
- Go 1.26 Enhances Type Checker: Cycle Detection Overhaul to Prevent Edge Cases
- Python's Official Blog Relocates to Open-Source Platform
- Mastering Multi-Agent Harmony: 10 Principles for Scaling AI Collaboration
- 6 Reasons Why You Should Verify, Not Just Trust, Your Software Supply Chain
- Streamlining Client Feedback: How AI and Open Source Transform Backlog Management
- Mastering Python Testing: A Guide to unittest Basics and Best Practices
- Scaling Multi-Agent AI Systems: Overcoming Coordination Challenges in Large-Scale Deployments
- 10 Essential Insights into Python 3.15.0 Alpha 5